ACTIVE DIRECTORY MONITORING
StealthINTERCEPT®: MONITORS AND PREVENTS THREATS
IN REAL-TIME FOR ACTIVE DIRECTORY SECURITY COMPLIANCE
DETECTION, PREVENTION, AND ALERTING IN REAL TIME FOR ACTIVE DIRECTORY SECURITY COMPLIANCE
See threats, both malicious and accidental, as they happen. Get active directory monitoring alerts in real time or use blocking to ensure threats don’t become disasters.

DETECT THREATS
Detect threats with advanced authentication and file attack analytics to catch malware, ransomware, and bad guys on your network.

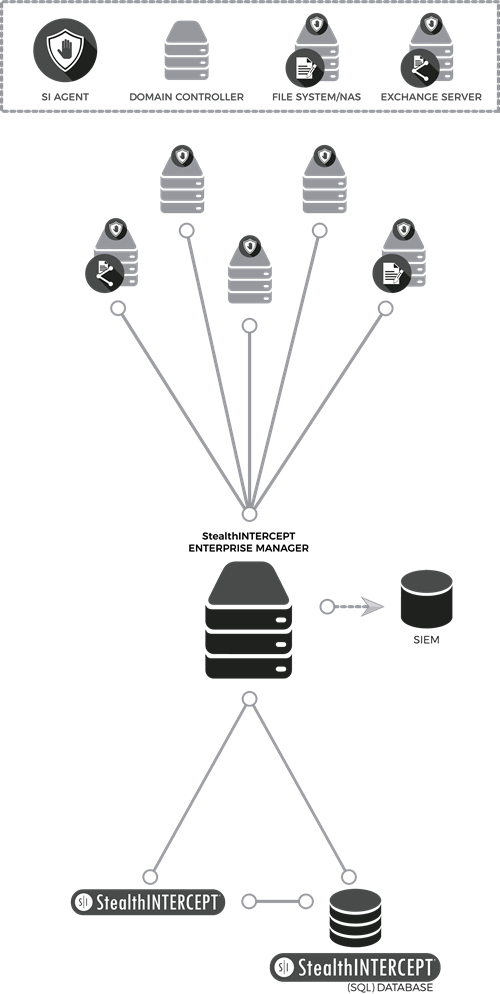
SKIP THE LOGS WITH SIEM
Integrate out of the box with the industry’s leading SIEM vendors. Increase the signal to noise ratio and get actionable insight in real-time.

ALERT IN REAL-TIME
Know when threats emerge, changes happen, people misbehave, or processes go rogue as it happens.

DETECT EVERY CHANGE IN ACTIVE DIRECTORY
Detect every change to group memberships, GPOs, Mailbox and File permissions, as well as access activities like critical file access and Non-Owner Mailbox Access Events without the need for a single log.

PREVENT CATASTROPHE
Prevent changes and access to sensitive objects and resources like privileged accounts and security groups, VIP Mailboxes, and File Shares containing sensitive data and more.

PREVENT OUTAGES
Migrating, upgrading, consolidating, or simply decommissioning a domain controller? Use surgical authentication analysis to know beforehand what you’re going to break.
StealthINTERCEPT Overview
WHAT’S NEW:StealthINTERCEPT 5.2 is Here!
ENTERPRISE PASSWORD ENFORCER
In 2016 the Verizon Data Breach Investigations Report (DBIR) stated that 63% of confirmed data breaches leverage a weak, default, or stolen password. The 2017 Verizon DBIR reported that 81% of hacking-related breaches leveraged either stolen and/or weak passwords. And in the 2018 DBIR, use of stolen credentials remains a number one action in breaches. Attackers have demonstrated a consist ability to compromise accounts by leveraging passwords from prior breaches. For that reason, NIST Special Publication 800-63B (Authentication and Lifecycle Management, section 5.1.1.2*) recommends the use of “Memorized Secret Verifiers” such as the StealthINTERCEPT Enterprise Password Enforcer to reduce an attacker’s chances of compromising credentials.
StealthINTERCEPT 5.2 expands on the capabilities of STEALTHbits Enterprise Password Enforcer to include:
Custom complexity – the ability to reject specific passwords that do not contain the characters from a set list. This is configurable on both the numeric and character level. Curated dictionary – the ability to reject passwords based on the fact that they are vulnerable to attack from a dictionary or hybrid cracking algorithm.
- Previous breach corpus – the ability to reject known compromised passwords from previous breach corpuses that are more susceptible to credential stuffing attacks.
- Length enforcement – the ability to reject passwords based on how many or few characters.
- User display/logon name rejection – the ability to reject passwords that are similar to the user’s display/logon name.
- Special character enforcement – the ability to reject passwords that do or do not contain specific characters.
- String rejection – the ability to reject passwords that contain user-defined strings (e.g. Reject passwords with “stealth” anywhere in the password).
- Incremental digit avoidance – the ability to reject passwords that end in a number.
- Keyboard pattern rejection – the ability to reject passwords that contain keyboard patterns (e.g. Qwerty)
- Sequential character rejection – the ability to reject passwords that contain sequential characters.
- Repeating character rejection – the ability to reject passwords that contain character repetition.
- Unique character enforcement – the ability to reject passwords that do not contain a minimum number of unique characters.
