eSentire Digital Forensics & Incident Response
DIGITAL FORENSICS & INCIDENT RESPONSE
Be Ready With the World’s Fastest Threat Suppression
Stop attackers in their tracks with our 4-hour remote threat suppression commitment so you can recover more effectively. eSentire Digital Forensics and Incident Response services are available for On‑Demand 24/7 Incident Response as a retainer offering, or for Emergency Incident Response support.
ESENTIRE ON-DEMAND 24/7 INCIDENT RESPONSE
Learn how eSentire’s On-Demand 24/7 Incident Response service gets you back to normal business operations in a matter of hours, delivering a guaranteed 4-hour threat suppression promise, anywhere in the world.
When a Data Breach Occurs, You Want Us In Your Corner.
Respond to any security incident with the world’s fastest threat suppression.
When disaster strikes, you need an incident response partner that can react with industry-leading speed and efficacy. Having immediate access to expert on-demand digital forensics and incident response services brings rapid control and stability to your organization when a breach occurs. How fast your organization contains and recovers from a security incident is critical to limiting business disruption, reducing costs, and recovering from
reputational damage.
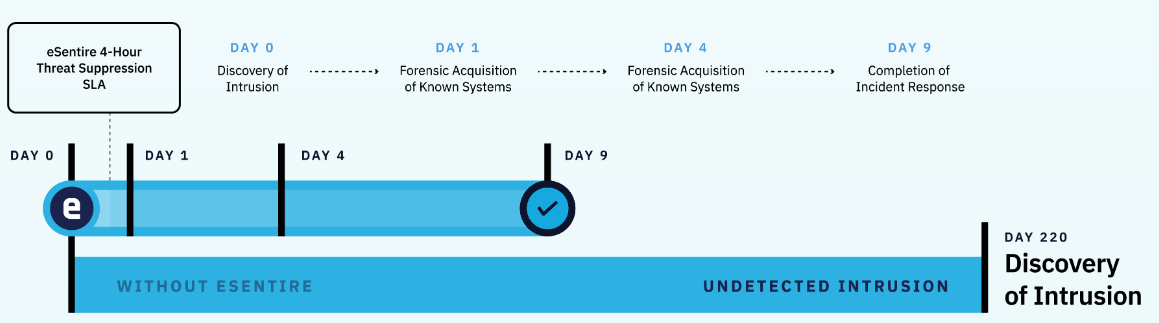
eSentire’s On-Demand 24/7 Incident Response service guarantees that you’re prepared for the most advanced attacks. Through a combination of best-in-class digital forensics technology and the expertise of our elite incident responders, we provide the fastest threat suppression in the industry, suppressing any incident, anywhere in the world, within 4 hours.
Our proprietary digital forensics tool, eSentire Agent enables rapid response so you can contain cyber threats and get back to normal business operations. Once our partnership begins, eSentire agents are deployed across your environment, giving our team instant access, detection and containment capabilities, delivering unmatched time-to-value.
eSentire’s Industry Leading 4-Hour
Threat Suppression
What You Can Expect
Industry-Leading 4-Hour Threat Suppression
OUR DIFFERENCE
Industry-Leading 4-Hour Threat Suppression
YOUR RESULTS
Get back to normal operations in a matter of hours with our guaranteed 4-hour threat suppression promise, anywhere in the world.
Our strategically deployed eSentire agent provides our team with immediate access to suppress any threat.
Elite Global Expertise, On-Demand
OUR DIFFERENCE
Elite Global Expertise, On-Demand
YOUR RESULTS
Priority access on-demand to our team of elite incident responders. No matter where you are, sleep easy knowing that a team of battle-tested cybersecurity experts with decades of technical leadership experience is standing by your side 24/7.
Breakthrough Digital Forensics Technology
OUR DIFFERENCE
Breakthrough Digital Forensics Technology
YOUR RESULTS
Experience immediate time-to-value and get back to normal business operations within hours (vs. days) through the use of industry-leading digital forensics and investigative tools, powered by the eSentire agent, no matter the size or location of your organization.
Full Support from Response to Recovery
OUR DIFFERENCE
Full Support from Response to Recovery
YOUR RESULTS
Get smooth recovery with full support through the investigative lifecycle, including the filing of cyber insurance claims, compliance & litigation evidence preservation, transitioning findings to law enforcement, supporting legal proceedings, expert witness testimony, and strengthening security gaps through the implementation of lessons learned.
Digital Forensics and Incident Response Services
eSentire Digital Forensics and Incident Response services are available for On-Demand 24/7 Incident Response or Emergency Incident Response support.
PROACTIVE On-Demand 24/7 Incident Response
Incident Response Retainer
- 4-hour threat suppression anywhere in the world
- Proprietary eSentire agent deployment across your network and IT systems the moment you on-board as a customer
- Rapid threat suppression within minutes of your call
With your On-Demand 24/7 Incident Response service, you may choose one of the following services each year:
Incident Response Plan Development
- Build an Incident Response Plan under the guidance of our cybersecurity experts
- By providing industry-specific templates
Incident Response Plan Assessment
- Review your current Incident Response Plan to make sure you’re prepared to withstand and recover from cyberattacks.
Tabletop Exercise (TTE)
- Assess the readiness of your IR effort with an annual tabletop planning and mock drill testing exercise
- Our experts provide recommendations for any necessary updates to your security program based on the results of the exercise.
REACTIVE Emergency Incident Response
Supporting the End-to-End Incident Response Lifecycle
- Rapid mobilization and deployment to quickly secure your systems and networks
- End-to-end incident management
- Managed threat containment
- Digital Forensic analysis collecting insights from your systems and networks
- Regression analysis to conclusively determine the full extent of compromised assets and determine root cause
- Incident recovery
- Determination of extent
- Stakeholder reporting
- Compliance support to meet regulatory requirements with centralized collection, retention and reports of log, network and endpoint data
- Litigation support as required
- Crisis communication support as required
Complete Cyber Incident Response
We deliver cutting-edge digital forensics, industry-leading threat intelligence, and powerful 24/7 Incident Response services and expertise. With our On‑Demand 24/7 Incident Response retainer in place, you can be confident you’re prepared for the most advanced cyberattacks.
4-Hour Remote SLA with Retainer
Quickly mobilizes investigative toolset and expert responders providing critical visibility and support across your affected networks and assets.
End-to-End Incident Management
Cyber Security Investigations team and supporting technologies cover the full incident response lifecycle.
On-Site Incident Responders
Within 24 hours, anywhere in the world, we can deploy boots on the ground for on-site incident response management.
Elite Tool Sets
To illuminate where attackers are present. Supports root cause analysis.
Managed Containment
Locks down and isolates threat actors preventing further spread and business impact.
Eradication Support
Identifies exploited vulnerabilities, supports remediation of affected assets.
Digital Forensic Analysis
Reconstructs the incident determining root cause, affected systems and attacker pathways.
Critical Visibility
Deployment of commercially available and open-source tools, including eSentire’s network, endpoint, and log technology, as needed, to collect endpoint telemetry, full network packets, netflow and log data from on-premises and cloud environments to provide multiple vantage points for analysis.
Asset Handling
Secure and robust processes for asset handling and chain of custody support.
Confirmation
Ensures the network is secure and monitors for attacker response and persistence measures.
Malware Analysis
We will detect and analyze malicious files and URLs for suspicious activities to gather a deep analysis and generate comprehensive & detailed reports.
Compliance Satisfaction
Meets regulatory requirements with centralized collection, retention and reporting.
Evidence Preservation
Gathers and stores incident details that meet legal, insurance and regulatory requirements.
Litigation Support
Expert and fact witness testimony, if needed, is available.
Robust Reporting
Detailed finding and impacts of the cyber investigation chronicle taken with lessons learned at the executive and technical level.
Incident Response eSummit
Build Resilience, Starting with Readiness.
As cyberattacks grow in scale and sophistication, downtime costs associated with cyber incidents can reach up to $225k per day. To reduce downtime and minimize recovery costs, security leaders need to ensure they are prepared to respond and contain a threat when a disaster strikes.
But traditional pre-breach preparation strategies may not be enough to ensure optimal response. It’s important that you meet your Incident Response provider and take care of any approvals and reviews before a cyber incident occurs. By achieving IR Readiness, you will be able to build cyber resilience, drive efficiencies throughout the incident response process, and get back to business faster.
Meet the eSentire Cyber Security Investigations Team
With the eSentire Cyber Security Investigations (CSI) team, you gain access to expertly trained incident responders, including computer forensic practitioners with decades of experience serving government intelligence agencies, federal and city law enforcement, the United States Military, and Fortune 500 companies.
Our team of responders has extensive digital forensics and incident response experience and multiple industry certifications:

eSentire CSI partners with our global 24/7 SOC Cyber Analysts and Elite Threat Hunters, extending your Digital Forensics and Incident Response support and expertise across hundreds of team members with deep knowledge of the tactics, techniques, and procedures (TTPs) adversaries use to break through your defenses.

eSentire’s Digital Forensics Technology Advantage
Our powerful eSentire agent makes our 4-hour threat suppression possible. This proprietary eSentire digital forensics tool enables our team to perform end-to-end investigations remotely and at unmatched velocity. We strategically deploy eSentire agents across your network and IT systems the moment you onboard as a customer. This allows eSentire to establish deep visibility and forensic capabilities in your environment before an incident ever occurs.
When a security incident requiring deep investigation does occur, you have the advantage. The agents give our Cyber Security Investigations team immediate access and forensic capabilities to actively start working within minutes of your call to suppress the threat in your environment. In 4 hours, the immediate threat will be suppressed and completely contained.
Benefits of leveraging the eSentire agent:
![]() Unmatched time-to-value
Unmatched time-to-value
![]() Unparalleled depth of visibility & investigation data
Unparalleled depth of visibility & investigation data
![]() Real-time visibility across all deployed assets
Real-time visibility across all deployed assets
![]() Accelerated incident response with reduced mean time to identify (MTTI) and mean time to contain (MTTC)
Accelerated incident response with reduced mean time to identify (MTTI) and mean time to contain (MTTC)
![]() Forensically-assured data at a fraction of the cost
Forensically-assured data at a fraction of the cost
![]() Support for remote work setting investigations with low-bandwidth connections
Support for remote work setting investigations with low-bandwidth connections
![]() e-Discovery and data collection for HR investigations, M&A activity, corporate security, and Personally Identifiable Information (PII) scanning
e-Discovery and data collection for HR investigations, M&A activity, corporate security, and Personally Identifiable Information (PII) scanning
![]() Trusted by government intelligence, federal law enforcement & military personnel
Trusted by government intelligence, federal law enforcement & military personnel
THE ESENTIRE AGENT
Watch this video to see how eSentire’s agent enables our 4-hour threat suppression SLA as part of our On-Demand 24/7 IR Retainer offering.
MDR + IR: A Recipe for Cyber Resilience in a Twenty-First Century Risk Landscape
As IT environments grow in complexity and organizations in nearly all industries undergo digital transformation, more confidential data is stored online, exposing you to increased cybersecurity risks. Today, organizations are increasingly targeted with a record-breaking number of cyberattacks from financially-motivated threat actors and sophisticated nation-state groups. It’s only a matter of time cyberattackers bypass your traditional cybersecurity measures.
To be able to anticipate, withstand, and recover from modern cyberattacks, you need a security solution that delivers real-time response, rapid threat containment, and remediation in case of an incident. Your security provider needs to go beyond alerts, extending their capabilities further into the incident response lifecycle to perform full-scale cyber investigation.
In this report, we share:
- Why it’s necessary to enhance your 24/7 threat detection, investigation, and response capabilities with Digital Forensics and Incident Response
- The benefits of combining MDR and Incident Response
- What to look for in an Incident Response provide
