Complete privileged access security for enterprises
ManageEngine PAM360
Comprehensive privileged access management solution
Privilege misuse is a top cybersecurity threat today that often results in expensive losses and can even cripple businesses. It’s also one of the most popular attack vectors among hackers, because when successfully carried out, it provides free access to an enterprise’s underbelly, often without raising any alarms until the damage is done.
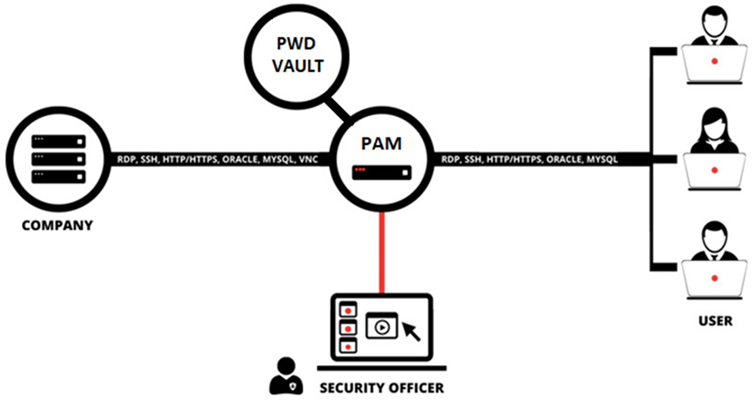
ManageEngine PAM360 empowers enterprises looking to stay ahead of this growing risk with a robust privileged access management (PAM) program that ensures no privileged access pathway to mission-critical assets is left unmanaged, unknown, or unmonitored.
PAM360 is a comprehensive solution for businesses looking to incorporate PAM into their overall security operations. With PAM360’s contextual integration capabilities, you can build a central console where different parts of your IT management system interconnect for deeper correlation of privileged access data and overall network data, facilitating meaningful inferences and quicker remedies.
Minimize security risks. Maximize business value.

Strict access governance

Central Control

Online reputation management

Regulatory Compliance

In-Depth event correlation

Smart workflow automation

Greater Visability

Enterprise credential vault
Scan networks and discover critical assets to automatically onboard privileged accounts into a secure vault that offers centralized management, AES-256 encryption, and role-based access permissions.

Secure remote access
Allow privileged users to launch direct, one-click connections to remote hosts without endpoint agents, browser plug-ins, or helper programs. Tunnel connections through encrypted, password-less gateways for ultimate protection.

Context-aware event correlation
Consolidate privileged access data with endpoint event logs for increased visibility and situational awareness. Eliminate blind spots in security incidents and make intelligent decisions with corroborating evidence.

Privileged session monitoring
Supervise privileged user activity with session shadowing capabilities and achieve dual control on privileged access. Capture sessions and archive them as video files to support investigative audits.

Privileged user behavior analytics
Leverage AI and ML-driven anomaly detection capabilities to spot unusual privileged activity at a glance. Closely monitor your privileged users for potentially harmful activity that might affect business.

Context-aware event correlation
Consolidate privileged access data with endpoint event logs for increased visibility and situational awareness. Eliminate blind spots in security incidents and make intelligent decisions with corroborating evidence.

Audit and compliance
Extensively capture all events around privileged account operations as context-rich logs, and forward them to your SNMP servers. Stay ever-ready for compliance audits with built-in reports for essential guidelines.

Comprehensive reporting
Make informed business decisions based on a range of intuitive, schedulable reports on user access and activity data. Generate reports of your choice by combining specific detail sets from audit trails to meet security mandates.

DevOps protection
Integrate password security into your DevOps pipeline, and protect your continuous integration and delivery platforms against credential-based attacks without compromising on engineering efficiency.

Ticketing system integration
Bolster your access approval workflows for privileged accounts by incorporating ticket ID validation. Authorize credential retrieval for service requests requiring privileged access only upon ticket status verification.

SSH key management
Discover SSH devices in your network and enumerate keys. Create and deploy new SSH key pairs to associated endpoints with a single click. Enforce strict policies for automated periodic key rotation.

Application credential security
Sanitize your application-to-application communications with secure APIs that eliminate the need for credential hard-coding. Shut down backdoors to your critical servers and keep attackers at bay.

SSL certificate management
Safeguard your online brand reputation with complete protection of your SSL certificates and digital identities. Integrate with popular certificate authorities like Digicert, GoDaddy, and Let’s Encrypt out of the box.