WHO WE ARE
Stealthbits Technologies, Inc. is a customer-driven cybersecurity software company focused on protecting an organization’s sensitive data and the credentials attackers use to steal that data. By removing inappropriate data access, enforcing security policy, and detecting advanced threats, our highly innovative and infinitely flexible platform delivers real protection that reduces security risk, fulfills compliance requirements, and decreases operational expense.
Identify threats. Secure Data. Reduce Risk.
Stealthbits’ Mission
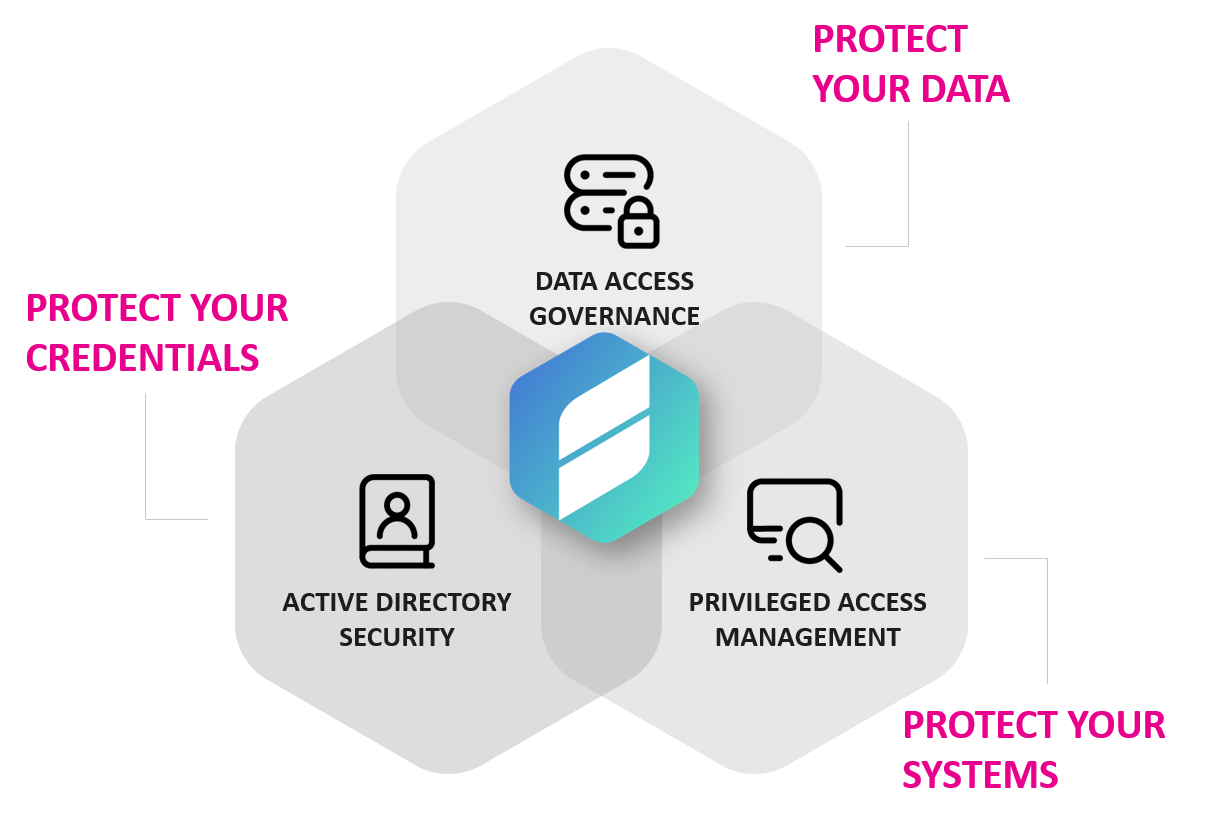
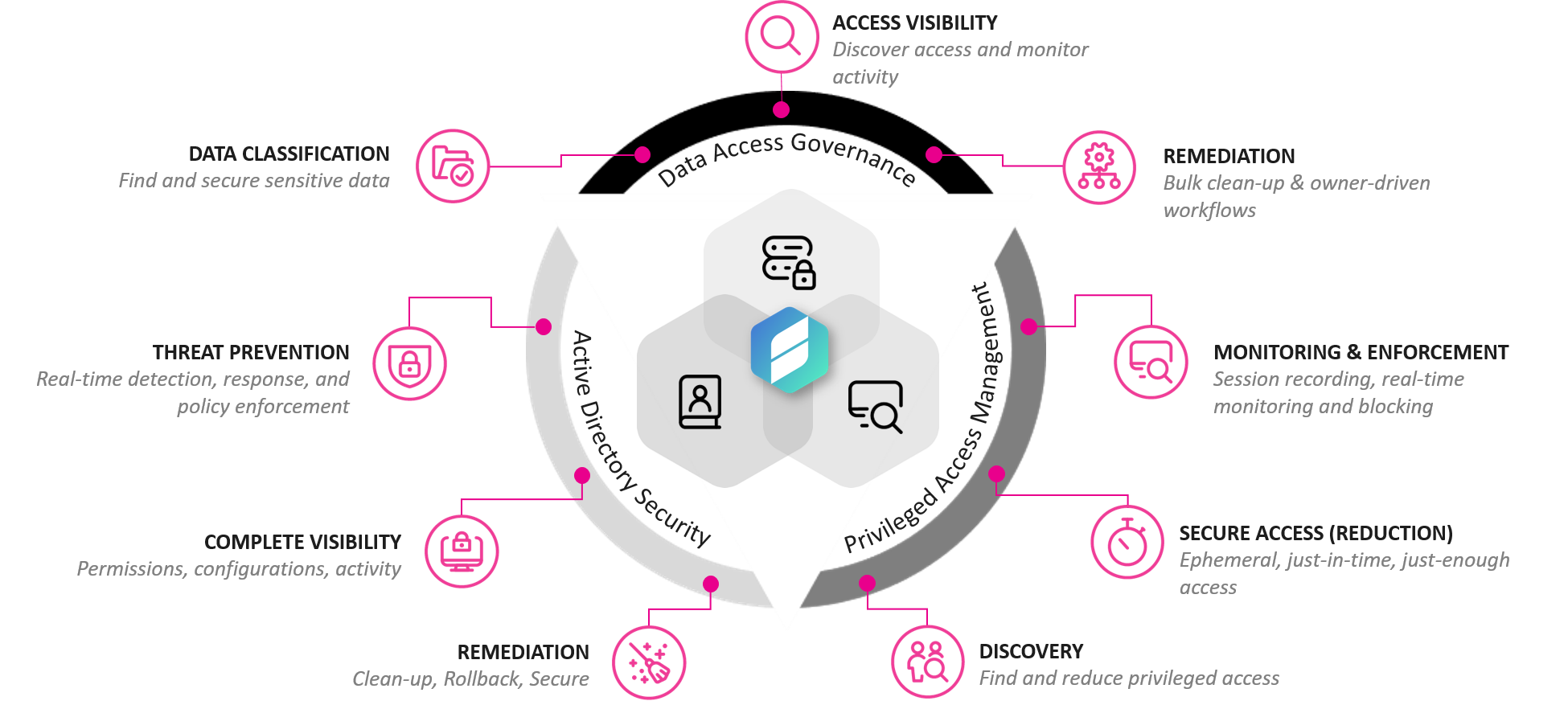
Stealthbits believes the security of your data is more than just understanding who has access to it. Data security relies on the security of Active Directory. The security of Active Directory relies on the security of the desktop and server infrastructure AD is most commonly compromised from. Stealthbits is the only provider that addresses each layer of the stack.
SOLUTION OVERVIEW
Credentials and data are the two common denominators in every breach scenario – credentials supply access to data. Credentials are valuable. Data contains information. Information is valuable. At Stealthbits, we help our customers secure their most sensitive data and the credentials that supply access to it. As a result, we provide the most comprehensive Data Access Governance, Active Directory Management & Security, and Privileged Access Management portfolio in the industry.
Product Overview
Protect your data: Reducing user access and permissions to data to the lowest levels possible limits exposure and risk, increases security, and reduces operational burden.
Protect your credentials: Ensuring Active Directory is clean, understood, configured properly, monitored closely, and controlled tightly, directly impacts data security, virtually wherever your data lives.
Protect your systems: Reducing “Standing Privileges” and remediating misconfigurations and vulnerabilities across desktop and server infrastructure mitigates risks like lateral movement and privilege escalation, keeping AD safe from advanced attacks.
Stealthbits’ technologies have been battle-tested and proven to meet the demands of the largest, most complex organizations in the world for nearly two decades. Our flexible, innovative, pragmatic approach to data security works and provides real results to real problems.

