Manage Logs | Audit | Secure | Be Complaint
Log management, auditing, and IT compliance
If you want to know what’s happening in your network to gain insights into potential threats and stop them before they turn into an attack, then you need to look into your logs. Let’s take a look at all the different log-generating aspects of an enterprise’s network:
- Perimeter devices such as routers, switches, firewalls, and IDS/IPS.
- Servers.
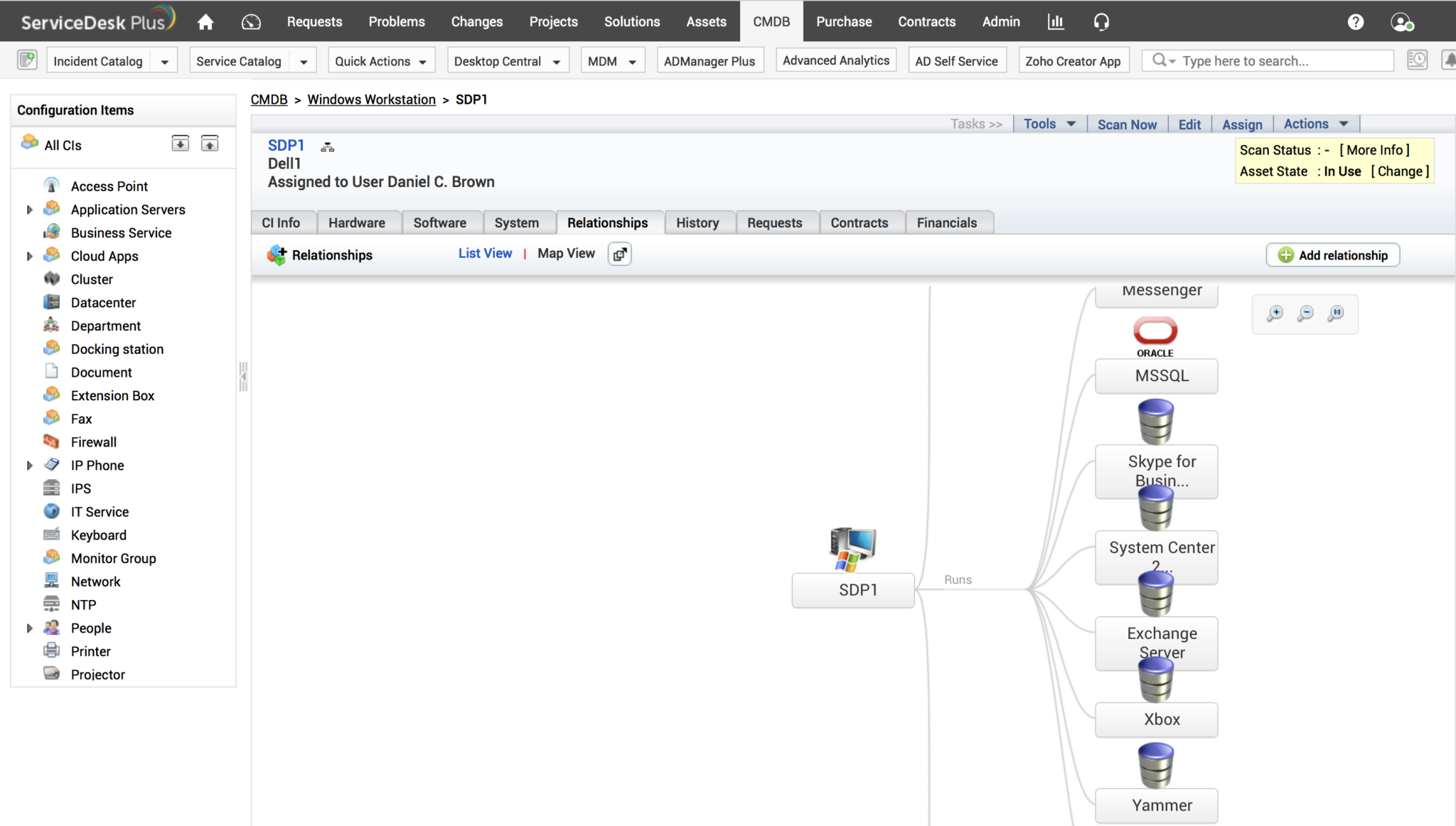
- Applications that your business runs, such as databases and web servers and more.
All these components generate an immense volume of log data. Manually sifting through logs from all these sources to find security events of interest, such as user accesses, unusual activities, user behavior anomalies, policy violations, internal threats, external attacks,data theft, and more, is futile.
What you can do with EventLog Analyzer

Real time event log correlation
Instantly detect attack attempts and trace potential security threats by correlating log data with over 30 predefined rules and a drag-and-drop custom rule builder. EventLog Analyzer comes with predefined rules to detect brute force attacks, account lockouts, data theft, web server attacks, and a lot more.
Raise a ticket in your help desk console for every correlation rule alert to ensure accountability and speed up incident resolution. EventLog Analyzer aggregates security events pertaining to a specific rule in a single report and provides a timeline view for effective security auditing.

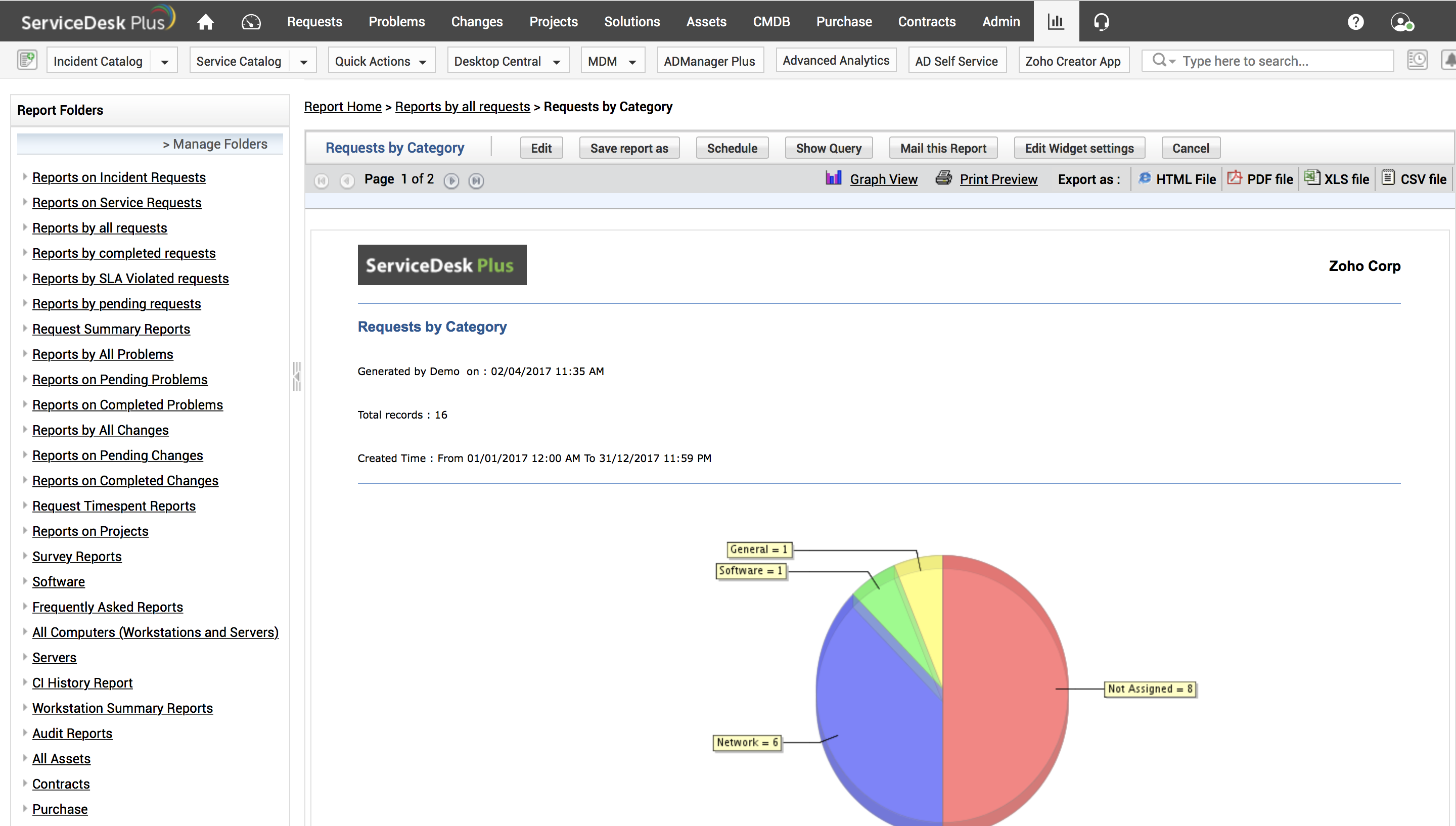
Integrated compliance management
Export comprehensive compliance reports in any format, tweak the existing compliance auditing report templates, or create completelynew compliance templatesto meet the demands of future IT regulations.

Augmented threat intelligence
Start detecting threats from malicious IP addresses as soon as you install EventLog Analyzer, no configuration required. With a built-in global IP threat database and STIX/TAXII feed processor, EventLog Analyzer helps identify any malicious IP address, URL, or domain interaction with your network in real time by automatically correlating log data with threat feeds.
EventLog Analyzer’s threat intelligencesystem is automatically updated every day to help you stay on top of threats and defend your network from the latest attacks. We’ve also integrated the threat intelligence system with the incident management feature to help you resolve incidents even faster.

Listen to your logs
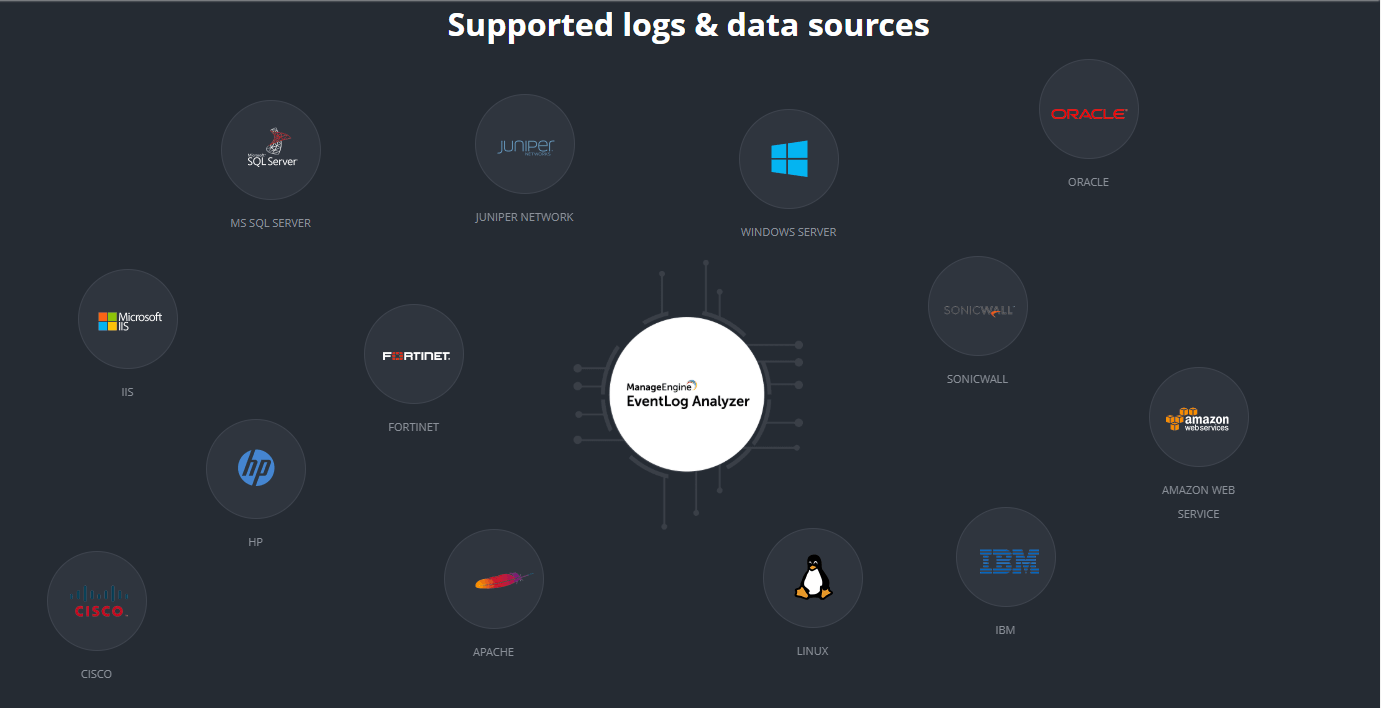
Collect, manage, analyze, correlate, and search through the log data of over 700 sources right out-of-the-box using:
EventLog Analyzer comes with a custom log parser that can extract fields from any human-readable log format. By managing logs from vulnerability scanners, threat intelligence solutions, data loss prevention applications, and a lot more, EventLog Analyzer truly offers a single console for viewing all your security log data.

Listen to your logs
EventLog Analyzer audits log data from perimeter devices, including, routers, switches, firewalls,
and IDS/IPS to provide valuable insights on:
- Firewall security policy and rule changes
- User logons and logoffs (including failed logons)
- Malicious inbound and outbound traffic
EventLog Analyzer presents all this (and a lot more) in intuitive, predefined reports. Further, you can set up alert profiles with predefined templates to catch anomalous events happening in your network.

Conduct in-depth application auditing
Audit critical changes, detect data theft, identify attacks, and track downtime in your business-critical applications, such as databases and web servers, with EventLog Analyzer’s application log auditing. With EventLog Analyzer, you can audit:
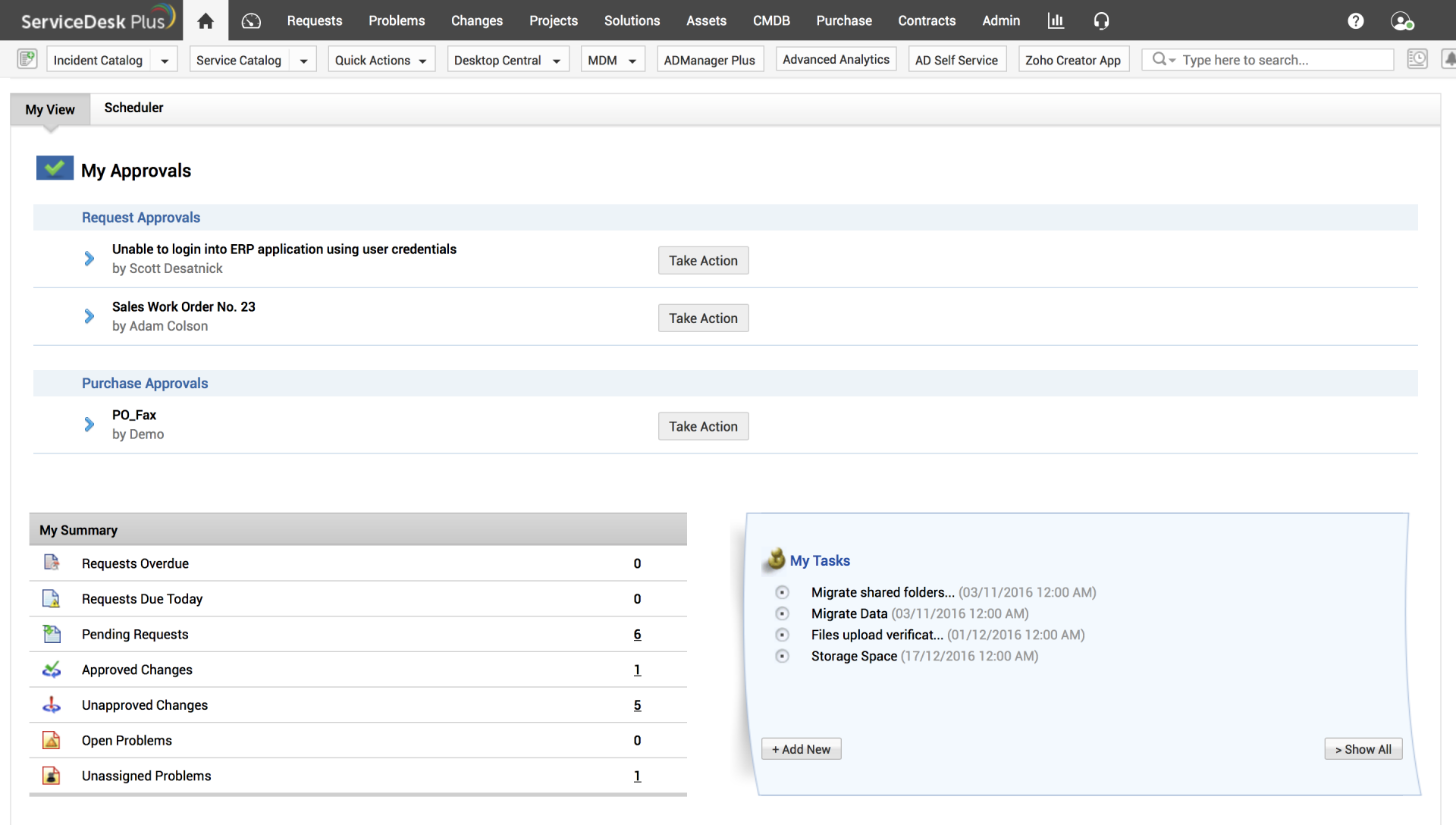
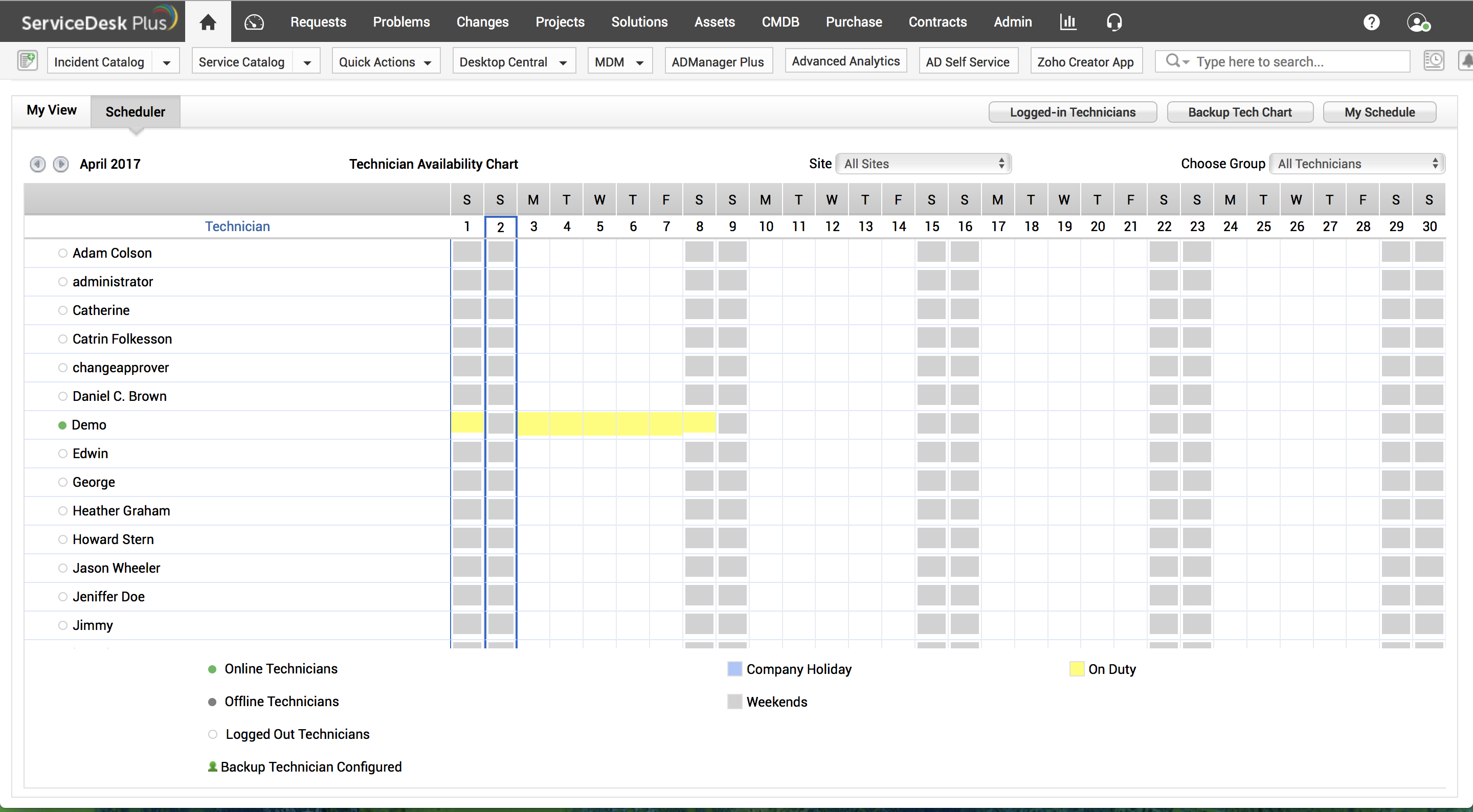
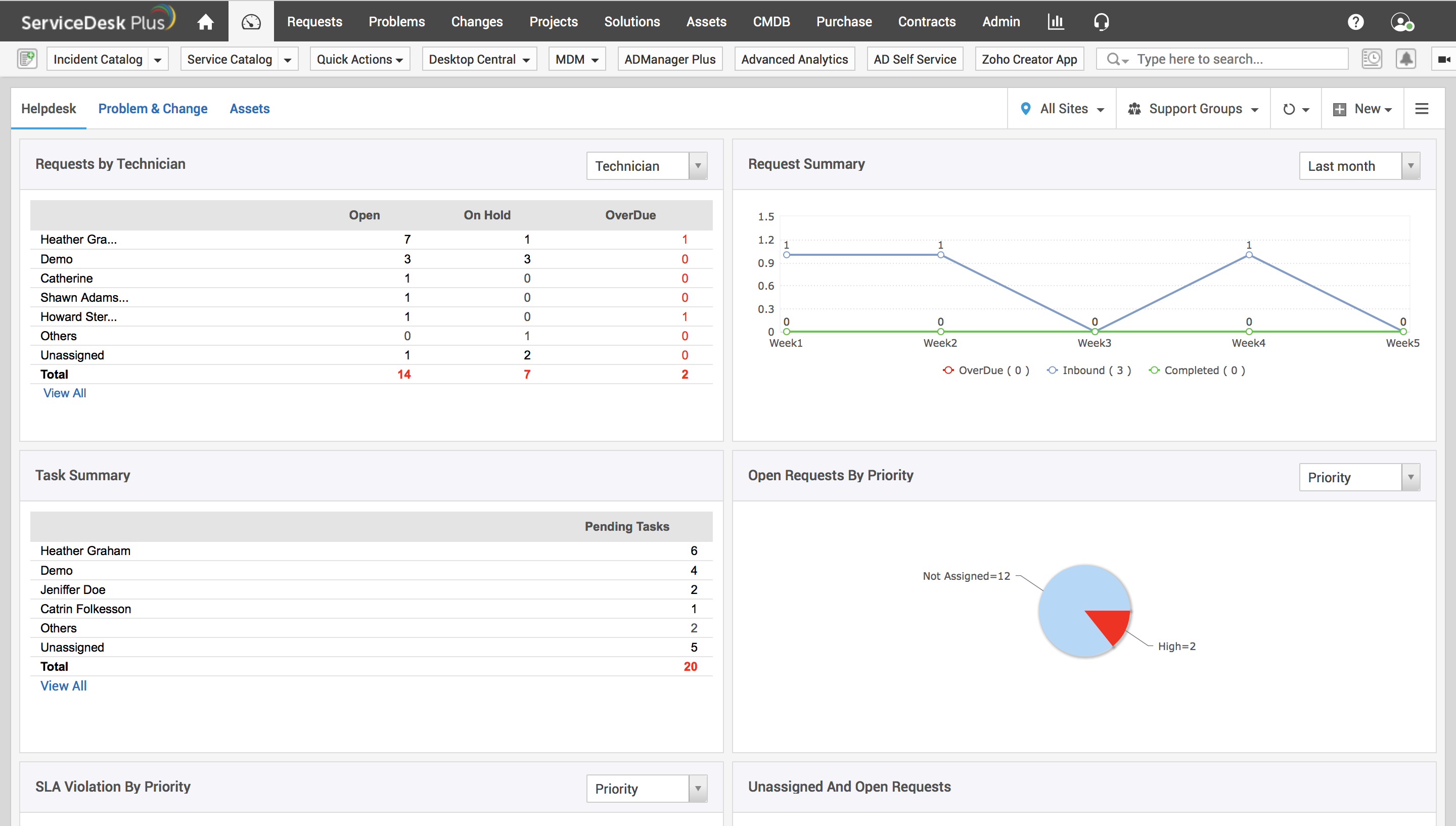
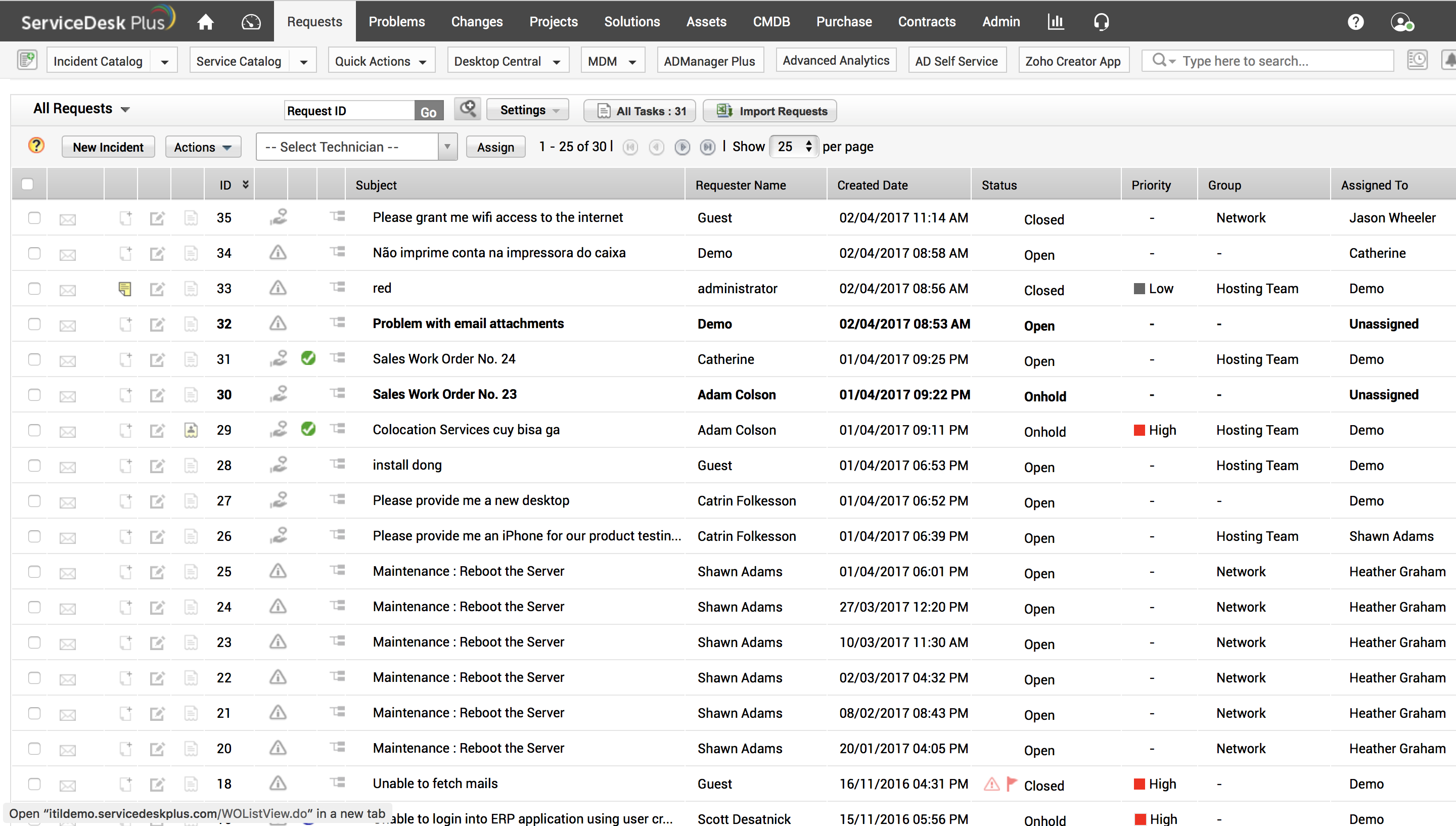
Dashboard Overview

Try EventLog Analyzer Plus For Free
- Access a single downloadable file for all 3 editions of ServiceDesk Plus on Windows or Linux machines
- Get a link to the live online demo
- Schedule a personalised one-to-one demo with one of our Product Experts
More Info
Office Hours: 9:00 – 18:00
Email: sales@sertalink.com
Phone: 32(0)3.337.17.01