Complete privileged access security for enterprises
ManageEngine PAM360
Uitgebreide beheeroplossing voor geprivilegieerde toegang
Privilege misuse is a top cybersecurity threat today that often results in expensive losses and can even cripple businesses. It’s also one of the most popular attack vectors among hackers, because when successfully carried out, it provides free access to an enterprise’s underbelly, often without raising any alarms until the damage is done.
ManageEngine PAM360 stelt ondernemingen in staat om dit groeiende risico voor te blijven met een robuust programma voor privileged access management (PAM) dat ervoor zorgt dat geen enkel geprivilegieerd toegangspad tot bedrijfskritische activa onbeheerd, onbekend of onbewaakt wordt gelaten.
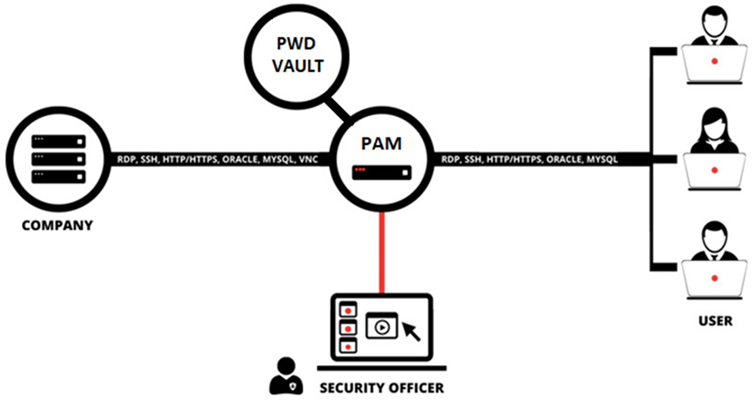
PAM360 is a comprehensive solution for businesses looking to incorporate PAM into their overall security operations. With PAM360’s contextual integration capabilities, you can build a central console where different parts of your IT management system interconnect for deeper correlation of privileged access data and overall network data, facilitating meaningful inferences and quicker remedies.
Minimaliseer beveiligingsrisico's. Maximaliseer de bedrijfswaarde.

Strikte toegangsbeheer

Centrale controle

Online reputatiemanagement

Naleving van de regelgeving

Diepgaande correlatie tussen gebeurtenissen

Slimme workflowautomatisering

Grotere zichtbaarheid

Kluis voor bedrijfsgegevens
Scan netwerken en ontdek kritieke activa om automatisch geprivilegieerde accounts in een veilige kluis te plaatsen die gecentraliseerd beheer, AES-256-codering en op rollen gebaseerde toegangsrechten biedt.

Veilige toegang op afstand
Sta bevoorrechte gebruikers toe directe verbindingen met één klik te starten met externe hosts zonder eindpuntagenten, browserinvoegtoepassingen of helperprogramma's. Tunnelverbindingen via gecodeerde, wachtwoordloze gateways voor ultieme bescherming.

Contextbewuste correlatie van gebeurtenissen
Consolideer geprivilegieerde toegangsgegevens met gebeurtenislogboeken van eindpunten voor meer zichtbaarheid en situationeel bewustzijn. Elimineer blinde vlekken in beveiligingsincidenten en neem intelligente beslissingen met ondersteunend bewijs.

Bevoorrechte sessiebewaking
Houd toezicht op de activiteit van geprivilegieerde gebruikers met schaduwmogelijkheden voor sessies en bereik dubbele controle over geprivilegieerde toegang. Leg sessies vast en archiveer ze als videobestanden ter ondersteuning van onderzoeksaudits.

Analyse van geprivilegieerd gebruikersgedrag
Maak gebruik van AI- en ML-gestuurde anomaliedetectiemogelijkheden om ongebruikelijke geprivilegieerde activiteiten in één oogopslag te herkennen. Houd uw bevoorrechte gebruikers nauwlettend in de gaten voor de mogelijk schadelijke activiteiten die van invloed kunnen zijn op uw bedrijf.

Contextbewuste correlatie van gebeurtenissen
Consolideer geprivilegieerde toegangsgegevens met gebeurtenislogboeken van eindpunten voor meer zichtbaarheid en situationeel bewustzijn. Elimineer blinde vlekken in beveiligingsincidenten en neem intelligente beslissingen met ondersteunend bewijs.

Audit en naleving
Leg alle gebeurtenissen rondom bewerkingen met geprivilegieerde accounts uitgebreid vast als contextrijke logboeken en stuur ze door naar uw SNMP-servers. Blijf altijd klaar voor nalevingscontroles met ingebouwde rapporten voor essentiële richtlijnen.

Uitgebreide rapportage
Neem weloverwogen zakelijke beslissingen op basis van een reeks intuïtieve, planbare rapporten over gebruikerstoegang en activiteitsgegevens. Genereer rapporten naar keuze door specifieke detailsets van audit trails te combineren om te voldoen aan beveiligingsvereisten.

DevOps-bescherming
Integreer wachtwoordbeveiliging in uw DevOps-pijplijn en bescherm uw continue integratie- en leveringsplatforms tegen op referenties gebaseerde aanvallen zonder afbreuk te doen aan de technische efficiëntie.

Integratie van ticketsysteem
Versterk uw werkstromen voor toegangsgoedkeuring voor geprivilegieerde accounts door ticket-ID-validatie op te nemen. Autoriseer het ophalen van inloggegevens voor serviceverzoeken waarvoor geprivilegieerde toegang vereist is, alleen na verificatie van de ticketstatus.

SSH-sleutelbeheer
Ontdek SSH-apparaten in uw netwerk en inventariseer sleutels. Creëer en implementeer nieuwe SSH-sleutelparen voor bijbehorende eindpunten met een enkele klik. Dwing strikt beleid af voor automatische periodieke sleutelrotatie.

Beveiliging van toepassingsreferenties
Maak uw applicatie-naar-applicatie-communicatie schoon met veilige API's die de noodzaak van hardcodering van inloggegevens overbodig maken. Sluit achterdeurtjes naar uw kritieke servers af en houd aanvallers op afstand.

SSL-certificaatbeheer
Safeguard your online brand reputation with complete protection of your SSL certificates and digital identities. Integrate with popular certificate authorities like Digicert, GoDaddy, and Let’s Encrypt out of the box.